
Topic
AI Risk & Security
Threats to models and systems, AI misuse, red teaming, and security posture
Featured


OpenAI Adds Personal Finance to ChatGPT with Bank Account Access
All Stories

Trump Orders Pre-Release AI Model Review Framework
President Trump signed an executive order Tuesday establishing a voluntary framework requiring AI companies to submit…

Anthropic scales Claude Mythos to critical infrastructure in 15 countries
Anthropic is expanding access to its Claude Mythos model and Project Glasswing security vulnerability program to 150…
Microsoft's OS-level sandbox aims to unlock enterprise AI agent deployment
Microsoft introduced Microsoft Execution Containers (MXC) at its Build conference, an OS-level sandbox built into…

AI Can Now Find Zero-Days. Your Patch Process Isn't Ready.
Anthropic's Claude Mythos model can autonomously discover zero-day vulnerabilities, closing a critical safety margin…

Illinois Passes AI Safety Audit and Whistleblower Bill
The Illinois House of Representatives passed legislation requiring major AI companies to submit model safety plans for…

Majority of AI Vendors Hide Subprocessors From Contracts
A DataGrail analysis of 2,400 business software vendors found that 63.6% of those advertising AI capabilities do not…

MFA Resets Become the New Attack Vector in Financial Services
Financial services organizations are being compromised through voice phishing and MFA resets rather than password…

The Hidden Cost of AI Debt in Enterprise Systems
Enterprise AI systems are accumulating new forms of technical debt across prompts, models, data pipelines, and…

White House, Anthropic Near Deal for U.S. Spy Agencies
The White House is negotiating a deal that would grant the National Security Agency and other U.S. intelligence…


The Blind Spot in Agent Governance: Untracked Cascading Failures
Autonomous AI agents in production are triggering infrastructure failures that engineering teams cannot categorize or…

MFA Stops at Login. Attackers Start There.
MFA successfully authenticates users at login but provides no visibility into what happens after, creating a critical…

Why AI Adoption Requires Brand Strategy, Not Just Tools
As content consumption reaches 12+ hours daily across platforms, production costs remain prohibitive, forcing companies…

AWS Demonstrates AI Recruitment Assistant Using Bedrock
AWS published a reference architecture for building an AI-powered recruitment assistant using Amazon Bedrock that…

GitHub Confirms 3,800 Repos Stolen in Supply Chain Attack
GitHub confirmed on May 20 that attackers compromised roughly 3,800 internal repositories through a poisoned VS Code…

White House Plans Pre-Release AI Model Review Framework
The White House Office of the National Cyber Director briefed major AI companies including OpenAI, Anthropic, and…

NanoCo AI Raises $12M to Build Secure Enterprise AI Assistants
NanoCo AI, founded by former Wix engineer Gavriel Cohen and his brother Lazer Cohen, has raised a $12 million…

Anthropic isolates agent credentials from execution to unlock enterprise deployment
Anthropic has released two new security capabilities for Claude Managed Agents that address a critical enterprise…

OpenAI Launches Content Provenance Tools to Verify AI-Generated Media
OpenAI has introduced a suite of tools focused on content provenance, including Content Credentials and SynthID, along…

Ocean raises $28M to deploy AI agents against email phishing
Ocean, an agentic email security platform, has raised $28 million to deploy AI that analyzes the full context of…

AI Supply Chain Blind Spot: Red Teams Miss Release Pipelines
Four supply-chain attacks hit OpenAI, Anthropic, and Meta within 50 days, exposing a critical gap in AI vendor security…

Torvalds: AI Bug Reports Are Drowning Linux Security List
Linus Torvalds has flagged a surge in duplicate security bug reports submitted to the Linux kernel mailing list,…

Google Bans AI Manipulation in Search Spam Policy
Google has expanded its spam policy to explicitly prohibit attempts to manipulate its AI systems in search results,…

Agent Authorization Gaps Widen as Deployment Accelerates
Cisco's chief security officer confirmed that rogue AI agent incidents are reaching enterprise customers, but the core…
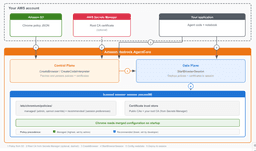
Bedrock AgentCore adds Chrome policies for controlled agent browsing
Amazon Bedrock AgentCore now supports Chrome enterprise policies and custom root CA certificates, enabling…

Anthropic's Mythos AI Shows Sharper Hacking Skills, U.K. Researchers Find
Researchers at the U.K.'s AI Security Institute reported Wednesday that Anthropic's latest version of Mythos AI…

Meta Launches Encrypted AI Chat with No Server Logs
Meta has launched Incognito Chat, a new AI conversation mode that Meta CEO Mark Zuckerberg claims offers end-to-end…

Supply Chain Attack Poisons 172 Packages with Valid Provenance
A supply chain attack dubbed Shai-Hulud compromised 172 npm and PyPI packages across 403 malicious versions starting…