AWS Adds Domain Filtering for AI Agents
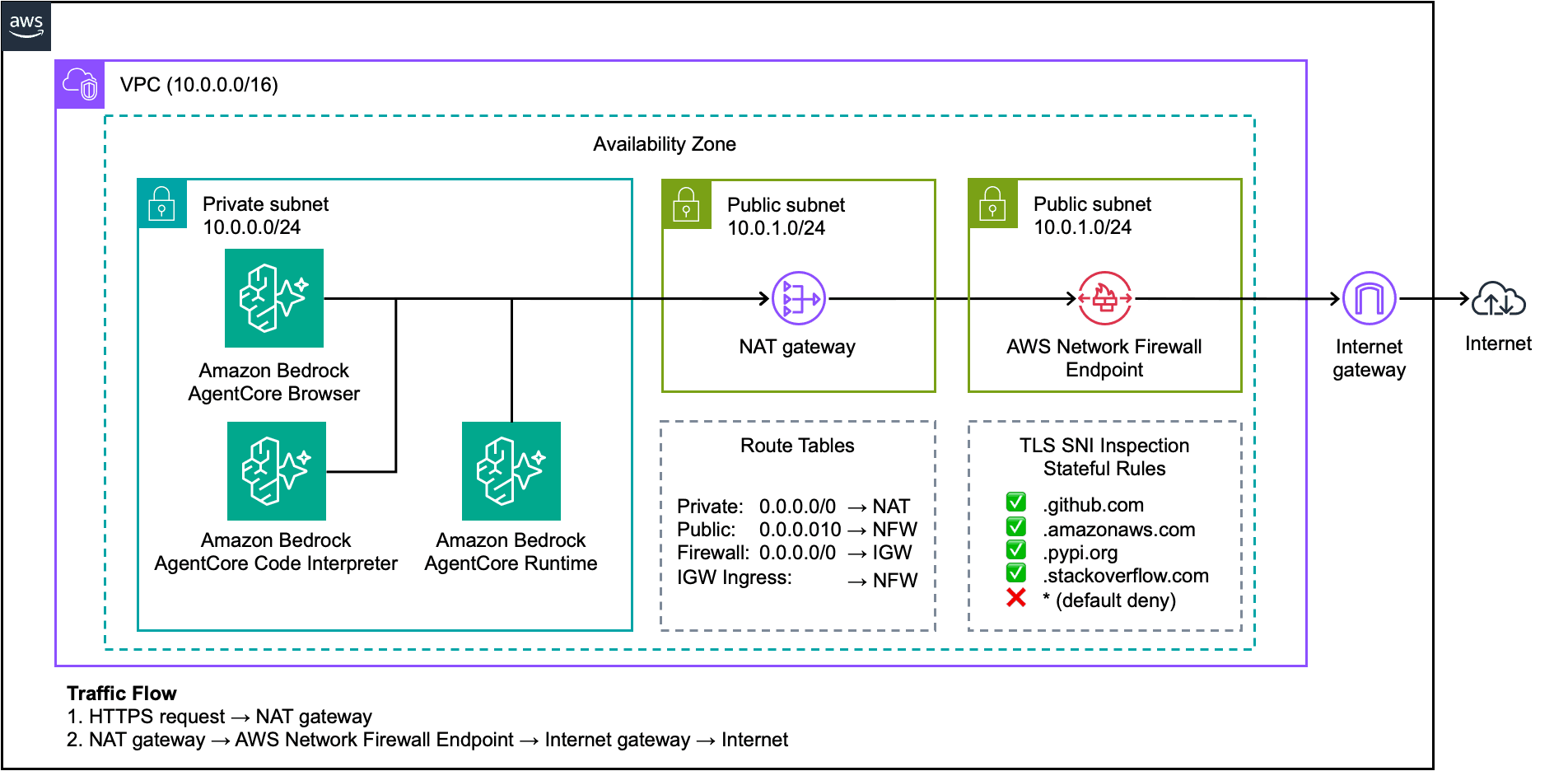
Amazon Bedrock AgentCore now supports domain-level access controls via AWS Network Firewall, allowing enterprises to restrict AI agent web browsing to approved domains. The capability addresses security and compliance concerns around unrestricted internet access, data exfiltration, and prompt injection attacks. Organizations can implement allowlists, block specific categories, log connection attempts, and apply default-deny policies to agent traffic when deployed in a VPC.
TL;DR
- →AWS Network Firewall can filter AgentCore agent traffic to approved domains using SNI inspection and domain-based rules
- →Enterprises can create allowlists (e.g., wikipedia.org, stackoverflow.com), block categories like social media, and log all connection attempts for audit trails
- →Multi-tenant SaaS providers can implement per-customer network policies with execution-specific blocking and regional restrictions
- →Default-deny policies and managed rules against botnets and malware domains reduce attack surface from prompt injection and unauthorized data access
Why it matters
AI agents with web access create new security and compliance risks for regulated industries. Domain-level filtering is a foundational control that enterprises require before deploying agents in production, addressing both data exfiltration concerns and prompt injection attack vectors. This capability moves agent security from theoretical to operationally feasible for risk-averse organizations.
Business relevance
For SaaS providers and enterprises deploying AI agents, domain filtering removes a major blocker in security reviews and regulatory approval processes. Multi-tenant operators can now offer per-customer network policies, expanding addressable markets in regulated verticals like finance and healthcare where network isolation is non-negotiable.
Key implications
- →Domain-level filtering becomes table stakes for enterprise AI agent deployments, shifting from optional to required security control
- →Multi-tenant SaaS platforms can now differentiate on security posture by offering granular, per-customer network policies that competitors without this capability cannot match
- →Prompt injection attacks become significantly harder to exploit when agents cannot reach arbitrary domains, reducing the practical threat surface of agent-based applications
- →Compliance and audit requirements around egress control and data exfiltration prevention become easier to satisfy with logging and allowlist enforcement
What to watch
Monitor whether other major cloud providers (Azure, Google Cloud) add similar domain-filtering capabilities for their agent platforms, as this could become a competitive baseline. Watch for emerging best practices around category-based rules and whether industry-specific rule templates emerge for regulated sectors. Track whether enterprises begin requiring these controls in vendor security questionnaires.
vff Briefing
Weekly signal. No noise. Built for founders, operators, and AI-curious professionals.
No spam. Unsubscribe any time.


